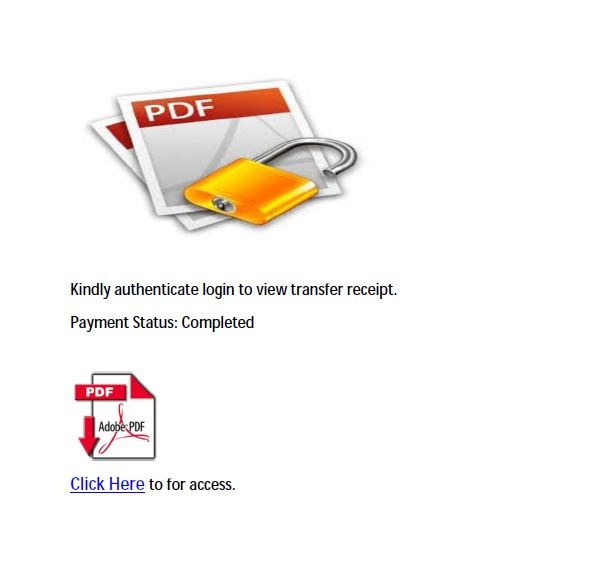
We all get emails from UPS, Walmart, Costco and other big retailers, airlines or travel resorts, but are they real?
Cybercriminals are always looking for ways to get your information, steal money or steal your identity. They will create emails that look like they are from your bank, the IRS, a store you shop at, coworkers, relatives, or friends.
These emails will contain links they want you to click so you can enter your information. Unfortunately, once you do that, the damage is done.
read more…





 and posing as an IRS agent – to sophisticated phishing scams that attempt to get taxpayers to reveal information that can be used to hack key user accounts.
and posing as an IRS agent – to sophisticated phishing scams that attempt to get taxpayers to reveal information that can be used to hack key user accounts.